Privacy Policy
1. Purpose of Personal Information Processing
The Korea Foundation (hereinafter, the Foundation) does not use personal information for any purposes other than the following purposes. The Foundation will seek prior consent of users before any changes to such purposes are made.
A. Membership Management
The Foundation collects a minimum amount of personal information required to provide customer services, handle complaints, and implement its programs.
B. New Service Development, Marketing, and Advertisement
The Foundation uses personal information obtained under law and with the consent of information subjects in satisfaction survey, statistics analysis, and smooth communication with customers to offer better services.
2. Collection and Retention of Personal Information
The Foundation collects and retains personal information under relevant laws and regulations and with information subjects’ consent only. Personal information files retained by the Foundation are as follows:
| File Titles | Processing Grounds & Purposes | Information Stored in Files | Retention Period |
|---|---|---|---|
| Website Membership Management File | Membership information management | Name, ID (e-mail address), password, and consent or refusal for e-mail communication | Until membership withdrawal |
| Information on Applicants for Online Social Science Data Services | Consent of information subjects | Name, e-mail address, contact information, mobile phone number, address, and complaintdetails | 5 years |
| Screening of applicant qualifications | |||
| Information on Complaint Submitters | Ethics and practice guidelines | Name, nationality, gender, occupation, department, major, e-mail, mobile phone number, andarea of interest | 2 years |
| Complaint handling |
3. Provision of Personal Information to Third Party
It is, in principle, prohibited to provide personal information retained by the Foundation to athird party, except the following cases:
A. For the purpose of collection, the Foundation may provide personal information to athird party when
- information subjects give additional consent,
- there are applicable laws or such provision is indispensable for fulfilling legal obligations,
- such provision is indispensable for conducting activities of public agencies specified by laws,
- or such provision is evidently necessary to protect the urgent interests of information subjects or athird party without prior consent because of incorrect address or because information subjects or theirlegal representatives are in no condition to express their opinion.
B. For other purposes, the Foundation may provide personal information to a third partywhen
except when there is a concern for unjust infringement on the interests of information subjectsor a third party
- information subjects give additional consent,
- there are special regulations specified in other laws,
- such provision is evidently necessary to protect the urgent interests of information subjects or a thirdparty without prior consent because of incorrect address or because information subjects or their legalrepresentatives are in no condition to express their opinion,
- such provision is necessary for the purpose of statistics and academic research, and in this case,information should be provided in a way that it cannot potentially identify a specific individual,
- activities specified by laws cannot be conducted unless personal information is used for other purposes orprovided to a third party (in this case, a protection committee’s prior deliberation and decision isrequired),
- it is necessary to provide information to foreign governments or international organizations to implementtreaties or international agreements,
- such provision is necessary to conduct crime investigation and prosecution,
- such provision is necessary for court proceedings,
- or such provision is necessary for the execution of a sentence, care and custody.
4. Entrustment of Personal Information Processing
When entrusting personal information processing, the Foundation abides by Article 26 of the Personal Information Protection Act. Accordingly, the Foundation stipulates, in a written , obligations and responsibilities, including the prohibition of personal information processing for purposes other than entrusted services, technical and managerial protection measures, restriction on re-entrustment, supervision of the entrusted party and compensation for damages, and supervises whether the entrusted party safely handles personal information.
| Entrusted Party | Entrusted Services | Period of Personal Information Retention and Use |
|---|---|---|
| INFO VALLEY KOREA | System maintenance and repair | Until membership withdrawal or end of entrustment contract |
5. Rights and Duties of Information Subjects and Methods to Exercise Them
Users may exercise their rights as Information Subjects as follows: The Foundation may entrust a third party with personal information processing under Article 26 “Restrictions on Personal Information Processing Entrustment” of the Personal Information Protection Act. The Foundation shall make an online announcement of relevant information including purposes, content and period of entrustment, and the entrusted party’s name, address and contact information.
A. Access to Personal Information for Inspection Under Article 35 “Access to Personal Information” of the Personal Information Protection Act, information subjects may request access to personal information retained by the Foundation.
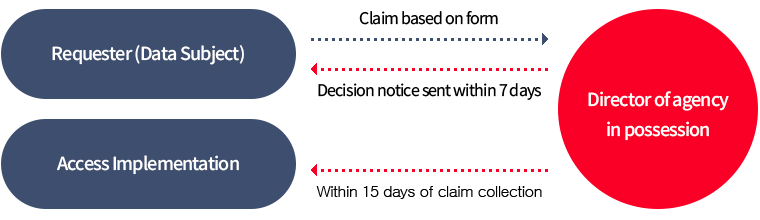
Requester (Data Subject)
Claim d on form
Decision notice sent within 7 days
Director of agency in possession
Within 15 days of claim collection
Access Implementation
- Requester (information subject) – Request using a form – Korea Foundation President
- Korea Foundation President – Notification of request results within 5 days – Requester (information subject)
- Korea Foundation President – Within 10 days after request collection – Access implementation
For application, please refer to the personal information access request form.Please be informed, however, access may be restricted in the following cases under Item 5, Article 35 of the Personal Information Act:
- Certain laws prohibit or restrict such access
- There is a possibility of harm to other people’s life or body, or unjustly infringement of their property or interests.
- There is a possibility of causing serious impediment to any of the following affairs of pubic organizations:
- Affairs related to the implementation of achievement, skill and recruitment examinations, and the screening of qualifications
- Affairs related to inspection and investigation in progress under other laws
B. Correction and Deletion of Personal Information
Information subjects may request the correction or deletion of personal information retained by the Foundation under Article 36 “Correction and Deletion of Personal Information” of the Personal Information Protection Act. They, however, are not allowed to make a request for the deletion of personal information if the collection of such information is stipulated under other laws.
- Scope of correction/deletion request
- Correction of information incorrectly recorded
- Deletion of content not applicable to certain categories
For application, please refer to the personal information correction/deletion request form.
- Procedures of request for correction or deletion.
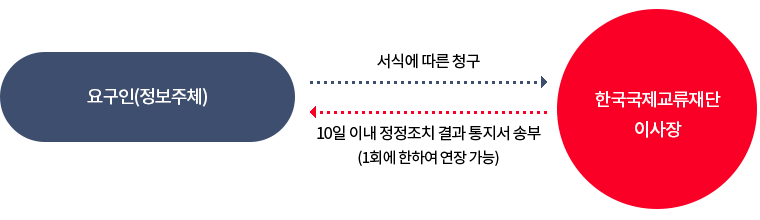
요구인(정보주체)
서식에 따른 청구
한국교류재단 이사장
10일이내 정정조치결과통지서 송부(1회에 한하여 연장 가능)
- Requester (information subject) – Request using a form – Korea Foundation President
- Korea Foundation President – Notification of request results within 10 days (may be extended just once) – Requester (information subject)
C. Discontinuance of Personal Information Processing
Information subjects may request the discontinuance of the processing of personal information retained by the Foundation under Article 37 “Discontinuance of Personal Information Processing” of the Personal Information Protection Act.
For application, please refer to the personal information access request form. The Foundation, however, may refuse to accept the request for the discontinuance of personal information processing under Item 2, Article 37 of the Personal Information Protection Act in the following cases:
- There are special regulations in laws or such refusal is indispensable for fulfilling legal obligations.
- There is a concern for unjust infringement of other peoples’ life, body, property, or other interests.
- Public organizations cannot implement their programs and activities stipulated by other laws if not allowed to process personal information.
- Personal information processing is needed to offer services and fulfill contract signed by information subjects who have not made clear their intention to terminate such contract.
D. Users may refuse to accept users’ agreement and privacy policy when signing up for membership. In this case, posting and the use of additional services may be partially restricted.
E. When signing up, users may fill in personal information selectively, if necessary. There is no disadvantage in receiving services in the case of such selective registration.
6. Types of Personal Information Processed
Please refer to the aforementioned “2. Collection and Retention of Personal Information” regarding the types of personal information processed by the Foundation.
7. Installation, Operation and Refusal of Automatic Data Collection Tool
A. Purpose of Using s
The Foundation uses s to offer better services to users by identifying website use pattern, number of users, and other information.
B. Installation, Operation, and Refusal of s
- Users have the right to choose the installation of s. They, therefore, may select options in their webbrowsers to allow the use of all the s, to confirm each time s are saved, or to refuse to save allthe s.
- When users refuse to save s, they may have difficulties in using some services that need login.
- Installation or refusal of s can be made with the following methods (in case of Internet Explorer):
- 1Select [Internet Options] from the [Tools] menu.
- 2Click the [Personal Information] tab.
- 3Set privacy level.
8. Disposal of Personal Information
When the personal information retention period has expired or processing purposes are achieved, the Foundation destroys personal information without delay in principle unless such information needs to be preserved under other laws. The process, timing, and methods of personal information disposal are as follows:
A. Disposal Process
In accordance with internal guidelines and relevant laws, the Foundation disposes of information entered by users when the retention period has expired or processing purposes are fulfilled.
B. Disposal Timing
Users’ personal information is destroyed within 5 days after the end date of the retention period or after it is deemed that the processing of such information is unnecessary due to the fulfillment of processing purposes.
C. Disposal Methods
The Foundation disposes of personal information in the following way:
- 1Information in electronic form shall be destroyed permanently in a way that it cannot be restored.
- 2Information in non-electronic form shall be destroyed by shredding or incineration.
9. Management of Message Board Information
To protect personal information, content in the Foundation’s message board (Contact the President, Q&A, and Policy Recommendations) is destroyed without delay two years after posting, and such disposal is recorded. Disposal records are managed by a department in charge of website maintenance.
10. Management of Dormant User Accounts
Dormant members are those who have not logged in for two years since they last logged in to the Foundation’s services. Such members’ accounts are considered dormant, and the Foundation may restrict their use of services offered by the Foundation. They need to go through authentication to use the Foundation’s services again after their accounts were classified as dormant ones.
11. Personal Information Protection Managers
The Foundation appoints personal information protection managers as follows to ensure appropriate collection and processing of personal information, thereby protecting users’ rights and interests and properly conducting programs and activities.
| Name | Phone Number | ||
|---|---|---|---|
| Senior Manager for Personal Information Protection | Jong-Kuk Lee, Executive Vice President of Finance and Operations | jklee@kf.or.kr | 064-804-1014 |
| Manager for Personal Information Protection | Bohyun Kim, Director, Resource Management Department | bhkim@kf.or.kr | 064-804-1061 |
| Staff Member for Personal Information Protection | Heejeong Kim, Senior Program Officer, Resource Management Department | privacy@kf.or.kr | 064-804-1064 |
12. Changes to Privacy Policy
When there are any changes made to its privacy policy, the Foundation shall announce such changes in its homepage to make them readily available to information subjects, and shall keep records of such changes in compliance with Article 30 “Establishment and Disclosure of Privacy Policy” of the Personal Information Protection Act.
Changes to Privacy Policy (January 31, 2012)
Changes to Privacy Policy (August 26, 2013)
Changes to Privacy Policy (December 22, 2013)
Changes to Privacy Policy (August 6, 2014)
Changes to Privacy Policy (February 5, 2015)
13. Measures to Secure Safety of Personal Information
Under Article 29 “Obligations for Safety Measures” of the Personal Information Protection Act, the Foundation takes technical, managerial, and physical measures for the safety of personal information as follows:
A. Restriction on Access to Personal Information
The Foundation controls access to personal information by granting, changing, and cancelling access rights to data system for personal information processing, and blocks unauthorized access by using firewall and detection systems.
B. Retention and Anti-Tampering of Access Records
The Foundation stores records of access to its website for at least six months, and makes sure such records are not tampered, stolen, or lost.
C. Technical Measures against Hacking
To prevent personal information leakage and damage by hacking or computer virus, the Foundation installs, renews, and checks safety programs on a regular basis, installs system in an access-restricted area, and conducts technical and physical surveillance and blocking.
D. Physical Access Control on Unauthorized Personnel
The Foundation has set up personal information system in a separate physical area, and controls physical access to the system d on its own access control procedures.
14. Remedy for Infringement on Rights and Interests
Information subjects may contact the Personal Information Dispute Mediation Committee, the Personal Information Protection Center of the Korea Internet and Security Agency, or other relevant organizations for counselling or dispute settlement regarding any infringement on personal information-related rights and interests. When they find counselling or remedy offered by the Foundation’s Personal Information Protection Managers unsatisfactory, they many inquire at the following organizations:
- Personal Information Dispute Mediation Committee: (without area code) 118 (Ext. 2)
- E-Privacy Mark Certification Committee: 02-550-9531 (www.eprivacy.or.kr)
- High-Tech Crime Investigation Department, Supreme Prosecutors’ Office: 02-3480-2000 (www.spo.go.kr)
- Cyber Terror Response Center, Korean National Police Agency: 02-392-0330 (www.ctrc.go.kr)